
|
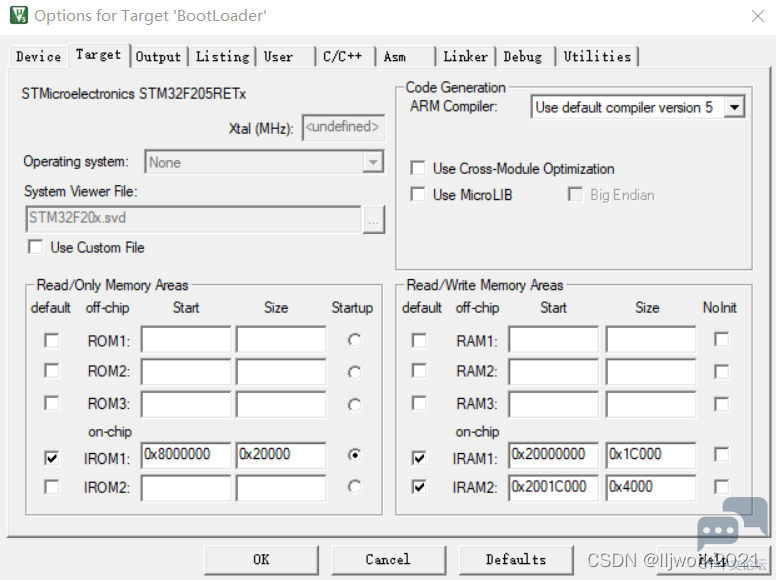
1. 简述 通过配置MDK,分别在不同地址写入BootLoader和App,BootLoader执行跳转函数,验证跳转App是否成功。 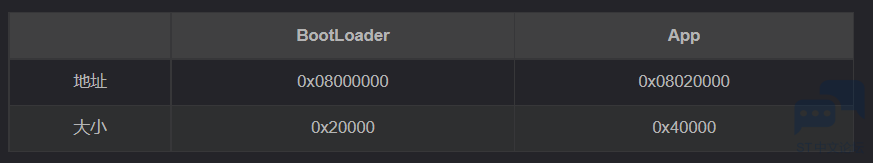
2. 跳转代码
BootLoader程序,执行bsp_iap_jump(0x08020000)函数,验证是否跳转到App执行。 ———————————————— 版权声明:lljwork2021 如有侵权请联系删除 |
分享STM32资料-采用 STM32U031R8 MCU 的 STM32 Nucleo-64 开发板,官方资料,数据手册等资料
HRTIM 指南
使用 STM32 的 DWT 单元监控内存
DAC,COMP,HRTIM Fault 功能的使用
一个软件引起的 LSE 驱动不良的问题
STM32 GUI LTDC 最大像素时钟评估方法
STM32 Cordic 运算速度评估
全新OpenSTLinux 6.1版本发布
ST-LINK Utility介绍、下载、安装和使用教程
【2025·STM32峰会】GUI解决方案实训分享1-对LVGL咖啡机例程的牛刀小试以及问题排查
 微信公众号
微信公众号
 手机版
手机版
